
Azure RACI Matrix for Enterprise Operations: Why Generic Templates Fail and What Actually Works
2024-01-01 · ~12 min read · Updated 2026-02-18
Generic RACI templates break in Azure because cloud operational ownership doesn't map to traditional IT roles. Here's how to build an Azure-specific RACI matrix across 8 operational domains that survives audits, scales past 10 subscriptions, and ends the 'who owns this?' argument.
Short answer: A standard IT RACI matrix does not work for Azure operations because Azure distributes operational ownership across identity, networking, security, cost management, monitoring, compliance, and workload domains that rarely align with a single team or job title. An effective Azure RACI matrix must define ownership at the task level within each domain, not the role level across the organization. Most governance failures in Azure are not policy failures — they are ownership failures where nobody was explicitly accountable for a specific operational task.
This guide is part of our Azure Governance hub covering policy enforcement, compliance frameworks, and enterprise controls.
Who This Is For
This article — and the matrix it documents — is built for enterprise Azure teams operating at scale.
Azure environments with 10+ subscriptions where informal coordination has broken down and operational ownership is ambiguous across teams, regions, or business units.
Organizations preparing for audit — SOC 2, SOX, FFIEC, ISO 27001, or internal audit — where evidence requests require named accountability, not team-level attribution.
Teams with shared services in hub-and-spoke topologies where the same resource type (firewall, DNS, monitoring workspace) is owned by the platform team but consumed by every workload team — creating accountability gaps at every boundary.
Platform teams struggling with ownership ambiguity — the recurring escalations where no individual has clear authority to act, and decisions stall because the RACI says "Cloud Team" instead of a person.
Mid-market to enterprise organizations with dedicated Azure roles (Platform Engineer, Security Engineer, Cloud Architect, FinOps Analyst) who need a structured baseline for cross-functional ownership alignment.
This framework is not designed for solo admins managing two or three subscriptions, or for personal lab environments. The structure is intentionally sized for environments where operational complexity requires documented accountability.
Preview
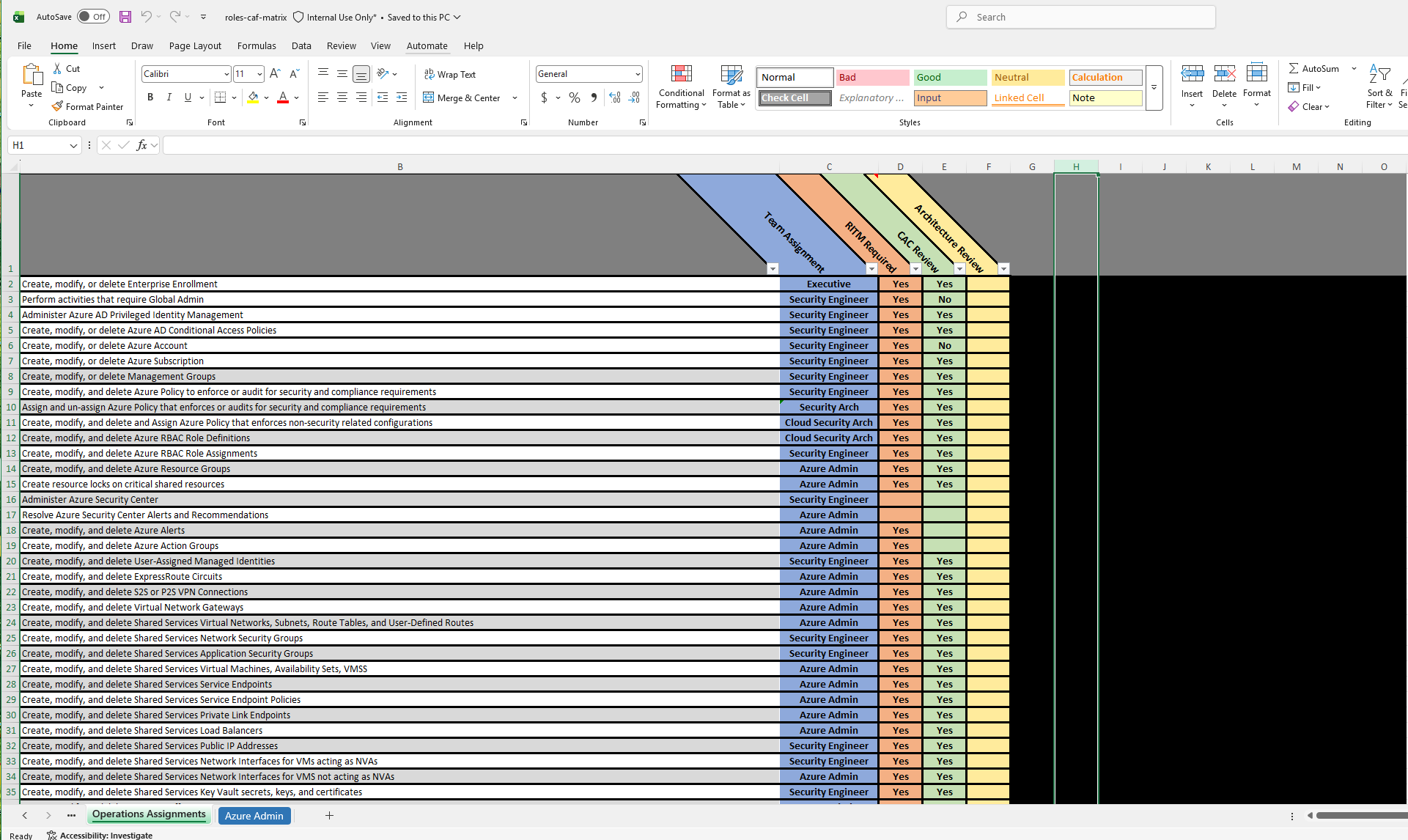
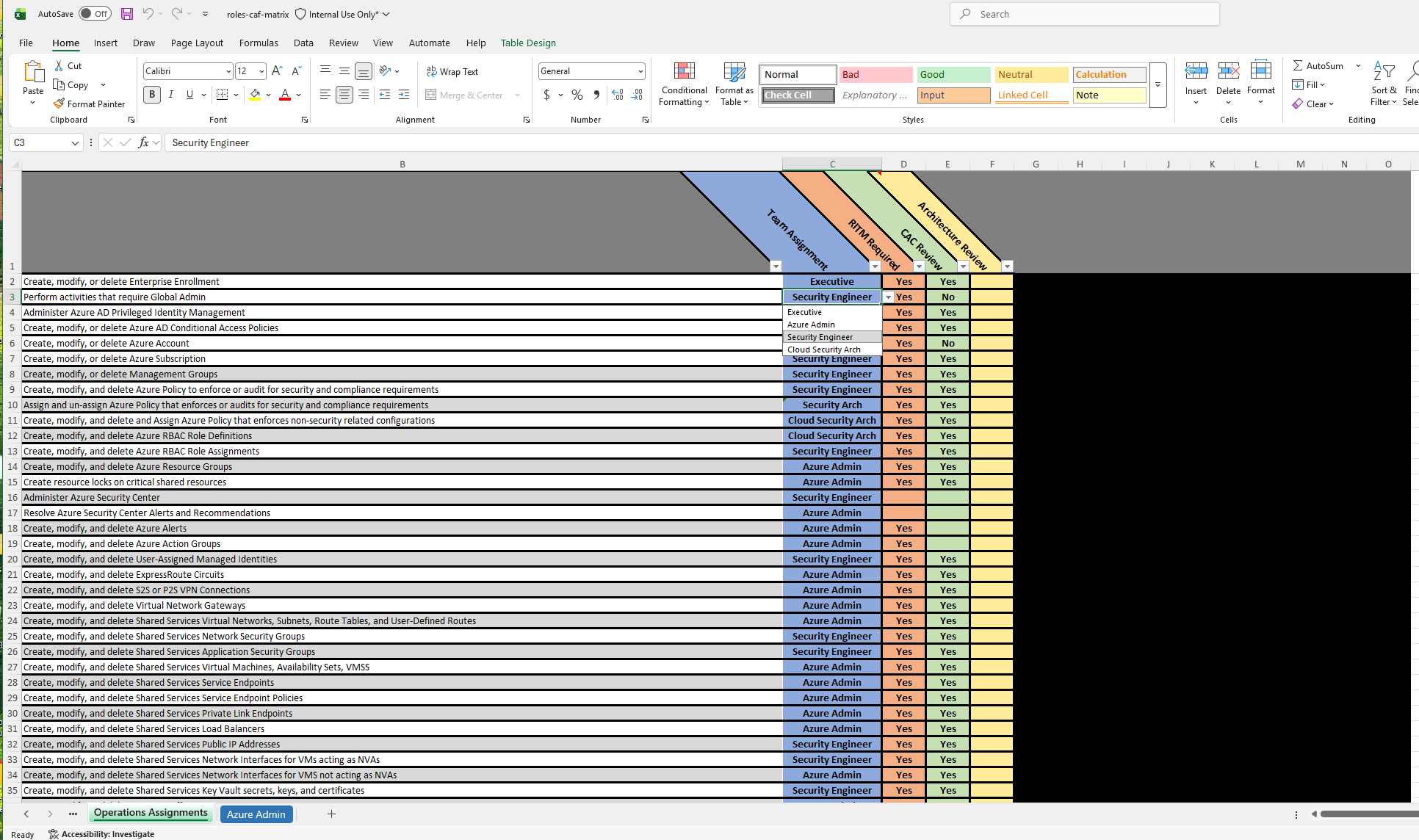
The matrix is structured as an Excel workbook with 58 operational tasks grouped across 8 Azure domains. Each task has a pre-assigned enterprise role — Security Engineer, Azure Admin, Cloud Security Architect, or Executive — reflecting how mid-to-large Azure teams actually divide operational work. Conditional formatting flags ownership gaps in red and conflicting dual assignments in yellow, so accountability problems are visible before an auditor sees them.
What You Actually Get
The Azure Cloud Operations RACI Matrix — 58 Pre-Assigned Enterprise Tasks (Excel Toolkit) is a single Excel workbook (.xlsx):
- 58 structured Azure operational tasks
- Organized across 8 operational domains
- Pre-assigned RACI roles (Responsible, Accountable, Consulted, Informed)
- Built-in gap detection via conditional formatting
- Excel (.xlsx) format — no SaaS dependency, no login required
- Fully customizable — every role, task, and assignment is editable
- Immediate download
- Version 1.0, updated quarterly
This is a populated, ready-to-customize workbook — not a framework document.
Perfect For / Not For
This workbook fits if your environment has:
- 10 or more Azure subscriptions
- Hub-and-spoke topology with shared platform services
- Active audit exposure: SOC 2, SOX, FFIEC, ISO 27001, or internal audit cycles
- Dedicated Azure roles — not one generalist handling everything
- Recurring ownership escalations across teams
Not a fit if:
- You manage two or three subscriptions
- Your environment is a lab, sandbox, or proof of concept
- You need a finished org chart that requires no customization
The Enterprise Azure Ownership Problem
Every Azure environment past 10 subscriptions has the same unspoken problem: nobody knows who is responsible for what at the task level.
Policies exist. Frameworks exist. Someone built a Confluence page that maps roles to responsibilities in broad strokes. The gap lives at the operational level — specific, recurring tasks that determine whether the environment is governed or just documented.
- Who renews the ExpressRoute circuit when the contract term ends?
- Who reviews Azure Advisor cost recommendations weekly — and who has authority to act on them?
- Who owns the decision to delete an orphaned resource group inactive for 9 months but still running $400/month?
- Who is accountable when a managed identity gets assigned Contributor at the subscription level instead of the resource group level?
- Who handles tag remediation when Finance rejects the chargeback report because 30% of resources have no cost center tag?
In most Azure environments, the honest answer is: nobody specific. Or worse — everyone assumes someone else is handling it.
Azure Policy cannot fix this. Policies enforce rules — they do not assign accountability for the human decisions that rules cannot automate.
What this gap costs in practice:
- Audit findings. An auditor asks who is responsible for reviewing privileged access quarterly and nobody can point to a name. The finding lands on the remediation tracker and stays there because the first task is determining who should own it.
- Cost overruns. Orphaned resources and untagged spend accumulate because cost optimization is "everyone's job" — which means it is nobody's job.
- Incident delays. A production workload fails. The escalation goes to the wrong team because the responsibility matrix says "Cloud Team" without specifying who owns networking versus identity versus compute.
Why Generic RACI Templates Fail in Azure
A traditional IT RACI matrix maps roles to functions. This works when infrastructure is static and siloed. Azure breaks it in three ways.
Tasks cross traditional role boundaries. Creating a Virtual Network is networking. Attaching an NSG is security. Routing through a firewall NVA is a firewall task. Peering to a hub is architecture. Tagging for cost allocation is FinOps. One resource, five domains. A generic row for "Virtual Network Management" assigned to "Network Admin" misses four of five accountability points.
Azure RBAC does not map to organizational roles. Built-in roles (Contributor, Reader, Owner) are permission sets, not job descriptions. Assigning RACI tasks to RBAC roles assigns accountability to permission levels, not to people.
Shared services create ownership ambiguity by design. Hub resources — firewalls, DNS zones, Log Analytics workspaces — serve every spoke subscription but are nominally "owned" by the platform team. A generic template has one row for "Firewall Management." An Azure-specific RACI needs separate rows for deployment, rule changes, performance monitoring, cost review, and certificate renewal — each potentially owned by a different person.
Microsoft's Cloud Adoption Framework defines capability functions but does not provide a task-level RACI. It intentionally stays at the capability level. Every enterprise independently builds the same task-level ownership framework — usually after a governance failure forces the conversation.
The 8 Azure Operational Ownership Domains
Identity & Access (Global Admin, PIM, RBAC) — Entra ID configuration, RBAC assignments, PIM activation policies, conditional access, managed identities, and service principal lifecycle. The domain where ownership gaps produce the most severe security consequences. Critical tasks: quarterly RBAC review, PIM approval workflow, service principal credential rotation, break-glass account testing.
Networking (NSGs, Private Endpoints, Firewall) — Virtual networks, peering, ExpressRoute/VPN, DNS, NSGs, route tables, and Private Endpoints. In hub-and-spoke topologies, ownership is split between platform and workload teams and must be explicit for each resource type.
Security & Defender — Defender for Cloud, Sentinel, security baselines, and compliance posture. The most common failure: Defender recommendations accumulate because nobody is assigned to triage them weekly.
Backups & Recovery — Backup policy validation, restore testing, cross-region replication, and failover procedures. Restore testing in particular requires an explicit owner and documented cadence.
Monitoring & Alerts — Azure Monitor, Log Analytics, alert rules, action groups, and diagnostic settings. Without an explicit owner for diagnostic settings standards, teams independently configure logging or skip it — producing inconsistent observability and unpredictable costs.
Key Vault & Secrets — Key Vault access policy review, secret rotation enforcement, certificate renewal, and managed identity credential lifecycle.
Subscription & Resource Governance — Azure Policy, management groups, subscription vending, naming conventions, and resource group lifecycle.
Change & Architecture Reviews — Change Advisory Board process for Azure infrastructure, architecture decision records, and design review ownership for platform-level changes.
Real-World Task Examples
| Task | Responsible | Accountable | Consulted | Informed |
|---|---|---|---|---|
| Quarterly RBAC review of subscription Owner/Contributor assignments | Security Engineer | Cloud Architect | Application Owners | CISO |
| Monthly cost anomaly investigation exceeding $500 threshold | FinOps Analyst | Cloud Architect | Workload Owners | Finance Director |
| Weekly Defender for Cloud recommendation triage | Security Engineer | Security Lead | Platform Engineer | Compliance Officer |
| ExpressRoute circuit health check and capacity planning | Network Engineer | Cloud Architect | ISP Account Manager | CTO |
| Tag remediation for resources failing cost allocation policy | Platform Engineer | FinOps Analyst | Application Owners | Finance |
| PIM role activation approval for production subscriptions | Security Lead | CISO | Cloud Architect | Audit Team |
| Azure Policy exemption request review and approval | Cloud Architect | Platform Engineering Lead | Security Engineer | Governance Board |
| Orphaned resource deletion approval (inactive >90 days) | Platform Engineer | Cloud Architect | Workload Owners | Finance |
| Break-glass account credential rotation and testing | Security Engineer | CISO | Cloud Architect | Audit Team |
Every row has exactly one Accountable person. "Cloud Team" does not appear in any row. A RACI matrix with team names instead of role titles is a document nobody can action because no individual owns the outcome.
Building This for Your Organization
Start with tasks, not roles. List every operational task that requires a human decision. You will find tasks nobody currently owns. That discovery is the point.
One accountable person per task. Not one team. One person by role title. If you cannot assign a single Accountable owner, the task is either too broad or the organization has not decided who owns that domain — a leadership conversation, not a spreadsheet exercise.
Include cadence. Every task needs a frequency: daily, weekly, monthly, quarterly, event-driven. A RACI row without a cadence will not happen consistently.
Separate hub from spokes. The same task type (NSG rule change) has different ownership depending on whether it is in the hub subscription or a workload spoke. The matrix needs separate rows for each context.
Test it against your last incident. Walk through the most recent operational incident your team handled. Verify every decision point had a clear owner. Gaps are incomplete documentation, not incomplete infrastructure.
The 60-Second "Accountable" Rule (So This Works in Your Org)
Most teams stall because they try to assign accountability to a team. Audits don't accept that. Pick one title per domain.
Use this baseline mapping if your org is missing specialized roles:
- Identity & Access: Security Engineer → if you don't have one, use Cloud Security Architect
- Networking: Network Engineer → if you don't have one, use Platform Engineer
- Security & Defender: Security Lead → if you don't have one, use Cloud Security Architect
- Backups & Recovery: Platform Engineer → if you don't have one, use Azure Administrator
- Monitoring & Alerts: Platform Engineering Lead → if you don't have one, use Cloud Architect
- Key Vault & Secrets: Security Engineer → if you don't have one, use Cloud Security Architect
- Subscription & Resource Governance: Cloud Architect → if you don't have one, use Platform Engineering Lead
- Change & Architecture Reviews: Cloud Architect → if you don't have one, use Architecture Review Board Chair / Director-level owner
The rule: one Accountable owner per task. If you can't name one, split the task or escalate the ownership decision — don't leave it ambiguous.
What Changes When Ownership Is Explicit
Audit responses accelerate. When an auditor asks who reviews privileged access quarterly, you point to a name, a cadence, and evidence of execution. The finding never reaches the remediation tracker.
Escalation paths become predictable. The matrix defines who owns hub networking versus spoke networking, and escalations follow the ownership rather than Slack channel intuition.
Cost waste decreases because orphaned resource remediation has an explicit owner with a defined cadence. "Someone should clean this up" becomes a named task with a named reviewer.
Cross-team disputes resolve faster because the ownership question was answered when the RACI was built — not at 3 AM during an incident.
Audit & Compliance Alignment
In regulated environments, a RACI matrix is not just an operational clarity tool. It is audit evidence.
Why team-level ownership fails. When an auditor asks "who is accountable for reviewing privileged access quarterly," the answer "the cloud team" is a finding — not a control. Audit frameworks require a named individual, a defined cadence, and demonstrable evidence of execution.
How task-level ownership maps to control frameworks:
- SOC 2 — access control reviews, change management procedures, incident response ownership, logical access provisioning/deprovisioning
- SOX — financial system access reviews, segregation of duties for cost management and chargeback, change approval authority
- ISO 27001 — asset ownership, access control policy, operational procedures, supplier relationship management
- Internal audit — evidence of control execution, ownership documentation, and control cadence verification
Named accountability plus cadence equals a defensible control. A RACI row that says "Security Engineer reviews subscription-level RBAC assignments quarterly, accountable to Cloud Architect" maps directly to an audit control. The same task assigned to "Cloud Team" does not.
This does not replace a formal controls framework. It provides the ownership layer that controls frameworks assume exists but rarely prescribe.
An enterprise Azure environment with 10–50 subscriptions generates 50–80 distinct operational tasks requiring explicit RACI assignments. Cataloging those tasks, reaching cross-functional agreement, and producing a format that survives the first audit request takes most teams two to four weeks.
The Azure Cloud Operations RACI Matrix — 58 Pre-Assigned Enterprise Tasks (Excel Toolkit) is a $49 starting framework — not a finished org chart. It eliminates the blank-page problem and provides a documented baseline for teams to customize against their own organizational structure. The pre-assigned role mappings are a starting position for the ownership conversation, not a prescription.
For teams in active SOC 2, FFIEC, SOX, or internal audit cycles: ownership is documented before the auditor asks. Gap detection surfaces unowned tasks before they become findings. The customizable format means the matrix adapts to your structure rather than requiring your structure to adapt to it.
Policy enforces.
Monitor finds.
Ownership fixes.
Related Posts
Azure Admin Starter Kit (Free Download)
Get my KQL cheat sheet, 50 Windows + 50 Linux commands, and an Azure RACI template in one free bundle.
Get the Starter Kit →💰 Stop Guessing at Azure Costs
Get the Azure FinOps Framework with cost allocation templates, tag governance policies, and showback dashboards that finance actually understands.
Download FinOps FrameworkExcel template • KQL queries included • No email required
